Understanding Identity and Access Management (IAM)¶
Identity and Access Management (IAM) is the security discipline that enables the right individuals or entities to access the right resources at the right times and for the right reasons. In the context of cloud security, IAM is a cornerstone for protecting sensitive data and ensuring the principle of least privilege is enforced. It provides the framework for managing digital identities and controlling their access to cloud resources.
Core components of IAM:¶
- Users: These represent individual people or services that interact with your cloud environment. Each user has a unique identity that needs to be authenticated (verified) before they can be authorized (granted permission).
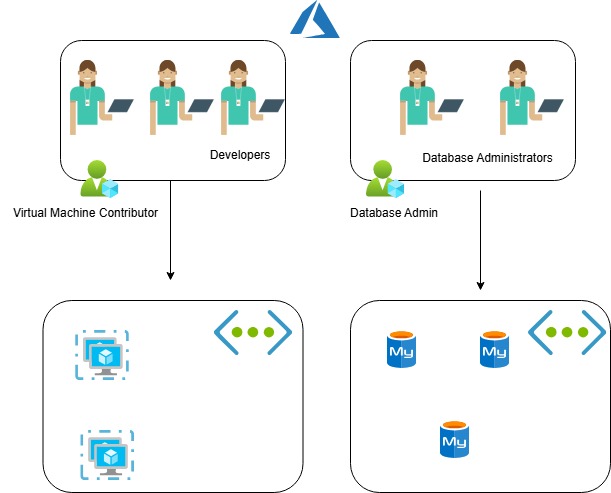
- Groups: Groups are collections of users that are managed together. Assigning permissions to groups simplifies the management of access for multiple users with similar roles or responsibilities. Instead of managing permissions for each user individually, you manage them at the group level.
- Policies: Policies are sets of rules that define what actions users or groups are allowed or denied to perform on specific resources. These policies are attached to users, groups, or resources to enforce access control. Policies are the heart of authorization in IAM.
- Policy Assignment: This refers to the act of attaching policies to users, groups, or resources. When a user attempts to access a resource, the IAM system evaluates the policies associated with that user (and their groups) and the resource to determine if the action is permitted.